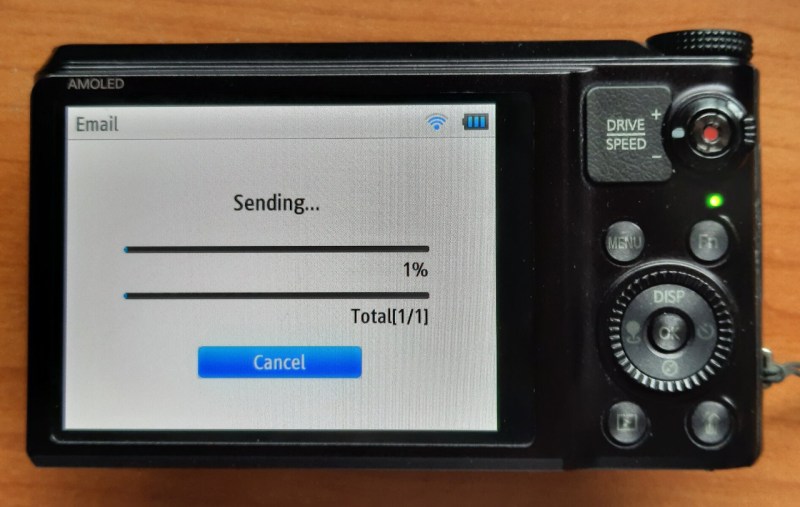
If your old camera’s WiFi picture upload feature breaks, what do you do? Begrudgingly get a new one? Well, if you’re like [Ge0rg], you break out Ghidra and find the culprit.
from Pocket
via Did you enjoy this article? Then read the full version from the author’s website.